People are usually concerned about their Windows computers picking up malware, and infection is sometimes a worry on Android devices. But iPhone users don’t typically worry about viruses, leaving many wondering if an iPhone can get a virus or not.
Let’s examine this and answer the burning question: can iPhones get viruses or other form of malware?
How Your iPhone Protects Against Infection
iOS and iPadOS, the operating systems that power the iPhone and iPad, are inherently secure platforms. They contain a number of built-in controls to filter out the worst attacks.
App Store Reviews
If you want to install an app on your iPhone, you have to go through the App Store. This is Apple’s official place for iOS apps, and it’s the only method to install software on your iPhone (aside from special methods for developers). The term “walled garden” is often used for this security approach.
To keep the App Store safe, Apple reviews each app that’s submitted to the store for malicious code or other foul play. In theory, this means that every app on the store is safe. This isn’t always the case, as we’ll see shortly, but it removes the worst offenders before they have a chance to infect people’s devices.
OS Sandboxing
Even if a rogue app did make its way onto your iPhone, it couldn’t do very much. iOS makes use of sandboxing, which basically prevents apps from touching data from other apps or the operating system itself. For example, a malicious app couldn’t freely read all of your contact data or see what other apps you have installed.
Most iOS apps don’t run as an administrator, further limiting their possibility for damage.
Frequent iOS System Updates
As we’ve mentioned before, installing OS updates is one of the best ways to protect all of your devices. Apple and other companies work to patch known vulnerabilities as soon as they can. While updates might not always bring new visible features, they protect your device behind the scenes.
Thankfully, the iPhone is much better at this than Android. When Apple issues an iOS update, everyone with a compatible device receives it around the same time. Android’s system update setup is fragmented, meaning you might not get important updates for months after they become available.
Historical Examples of iPhone Malware
While uncommon, instances of iPhone malware have happened. Most of these were only an issue in specific circumstances, which we examine below.
One of the biggest cases of iPhone malware was in 2015, known as XcodeGhost. Xcode is Apple’s development tool that allows programmers to create iOS apps. This issue arose when developers in China unknowingly downloaded infected copies of Xcode from Chinese servers.
Apps created with this compromised tool, which Apple later removed from the App Store, contained malware. Most of the affected apps were ones only utilized by Chinese users, but some were apps with worldwide appeal.
In 2017, scammers abused the pop-up function in Safari to “lock out” the user, demanding gift cards for payment. This is an example of a fake ransomware attack, as it didn’t actually encrypt anything. With iOS 10.3, Apple patched this to prevent the problem.
More recently, Apple removed 18 harmful apps from the App Store in October 2019. These apps were seemingly innocent offerings across several categories, but were actually acting maliciously without the user’s knowledge. After being installed, they continuously opened webpages in the background and clicked them to generate phony ad revenue.
While the worst effect this would have on the user is decreased battery life and maybe extra data charges, it illustrates that Apple’s controls aren’t always perfect.
Have a look at the Malware for iOS page on The iPhone Wiki for more examples of iPhone malware.
How to Avoid Getting an iPhone Virus
We’ve looked at what Apple does to keep iOS safe, and how examples of malware occasionally sneak in. Let’s close with some tips for keeping your own device protected from malware.
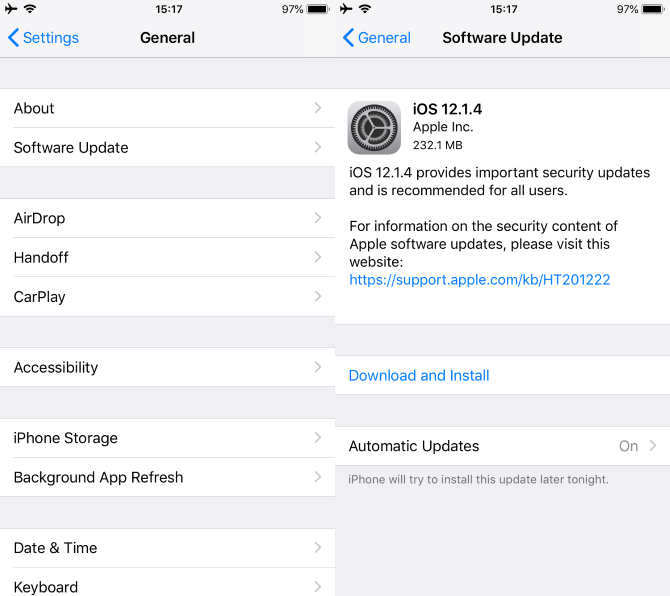
Keep iOS Up to Date
As mentioned above, installing security updates is vital for iPhone security. Head to Settings > General > Software Update to make sure you’re up-to-date, and don’t put off installing security patches when prompted.
We’ve written before about how your iPhone could become a digital spy or be controlled over Wi-Fi due to certain vulnerabilities. Updating your device is the quickest way to fix these.
Don’t Jailbreak Your Device
The majority of iPhone malware only works on jailbroken devices. If you’re not familiar, “jailbreaking” refers to using workaround methods to remove Apple’s restrictions on your iPhone. A jailbroken device can install apps from third-party sources and thus doesn’t enjoy the protections of iOS mentioned above.
Jailbreaking has fallen in popularity over time, so you probably don’t have any interest in it. Doing so is the quickest way to open up your iPhone to attack.
Only Install Apps You Trust
While the App Store is in general a safer place than the Google Play Store, you still shouldn’t blindly install apps on your iPhone. Avoid installing little-known apps that don’t have many reviews, especially if they contain typos or other red flags on their app page.
Stick to well-known apps as much as you can; it’s easier to deceive a small amount of users with a newer app.
Forget iPhone Antivirus Apps
As an extra measure of protection, you might think to install an antivirus app from the App Store. However, this is unnecessary. As mentioned above, iOS sandboxing prevents apps from touching data used by other apps. This means that “antivirus” apps can’t actually scan for infection like they can on Windows or Mac.
Most of these “antivirus” solutions include features that duplicate what your iPhone already offers. These include anti-theft location tools (you already have Find My iPhone) and protection from dangerous websites (which is built into all major browsers). There’s really no reason to use them; your iPhone already has all this in place.
Staying Safe on iOS
So, to answer the question, can iPhones get viruses? In summary, most people are very unlikely to ever pick up malware on their iPhone. As long as you don’t jailbreak, keep your device updated, and exercise some caution when installing apps, your iPhone will be virus-free. While no platform is perfect, Apple’s security designs in iOS are definitely solid.
For more on this, take a look at important iPhone security practices you should follow.
Image credit: Blogtrepreneur/Flickr