We’ve talked before about encryption, which is an essential part of modern digital life to keep your data secured. But there’s another type of communication encryption you’ve probably heard about too: end-to-end encryption.
Let’s find out how end-to-end encryption differs from other forms of encrypted conversations, and what it means for you when you use apps like Signal.
A Refresher on Encryption
In our overview of encryption, we discussed that encryption is essentially the process of taking data and making it unreadable to everyone except for the parties who are supposed to read it. It’s akin to scrambling a note with a secret code that only you and the recipient know, though it’s much more mathematically complex than this.
Encryption is present in many forms in the digital world. When you connect to a website that offers HTTPS, as most websites do today, nobody outside of your computer and the website’s server can view your activity. Protecting your Wi-Fi network with a password also encrypts the traffic on it.
Defining End-to-End Encryption
Encryption is used in a lot of cases, but it’s not used the same way in every instance. This is where end-to-end encryption, which is typically used in communication, comes in. End-to-end encryption is a system where only the people communicating can decrypt and read the messages. Nobody else, whether they’re part of the process or not, can see the messages at any point.
In particular, this means that the server handling the messages cannot access the messages, even if it wanted to. This is important, as we’ll see next.
An Example Without End-to-End Encryption
Let’s take an example with a service like Facebook Messenger. Facebook Messenger offers what’s called client-server encryption, but messages you send on the service are not end-to-end encrypted.
Client-server encryption means that when you send a message, your message is encrypted when it goes from your device to Messenger’s servers. It’s protected with a key that only your device and the server know.
However, the message is decrypted on Facebook’s server, then re-encrypted when it’s sent from the server to the other person’s device. When the server re-encrypts the message, it uses a key that only it and the recipient know.
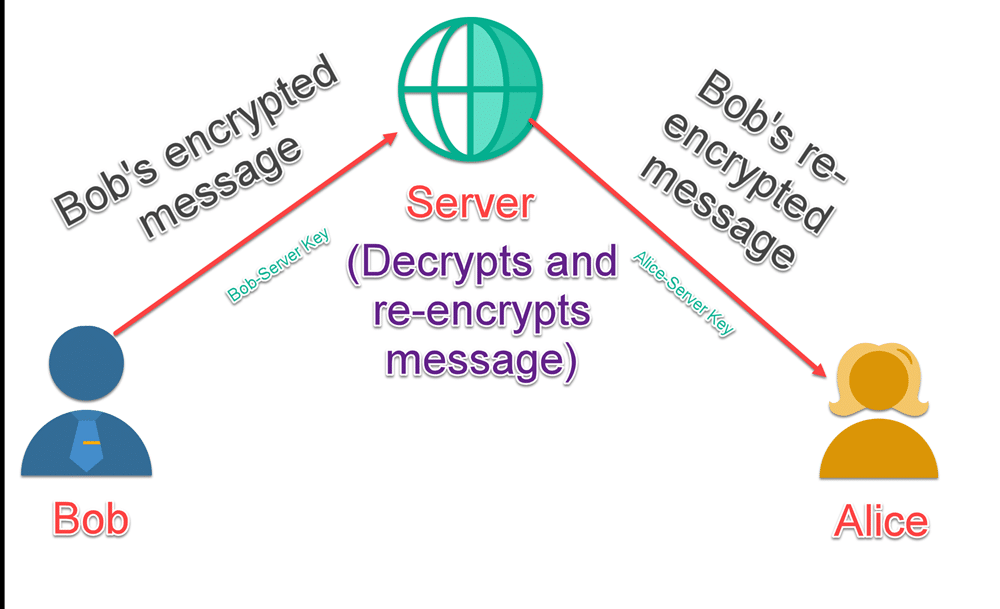
This protects your message while in transit, which is typically when a message is at its most vulnerable. It’s also convenient, as it allows you to access your Messenger conversations from anywhere that you’re signed in to your account. When you sign in to a new device, Messenger syncs all of the conversations it has stored for you to your new phone or computer.
However, this setup also poses a privacy risk. Because Facebook’s servers decrypt your message as part of the communication process, your message is vulnerable at that point. If the server was hacked, the attacker would likely be able to read all of your messages. And if Facebook wanted to, it could read your messages too.
How End-to-End Encryption Differs
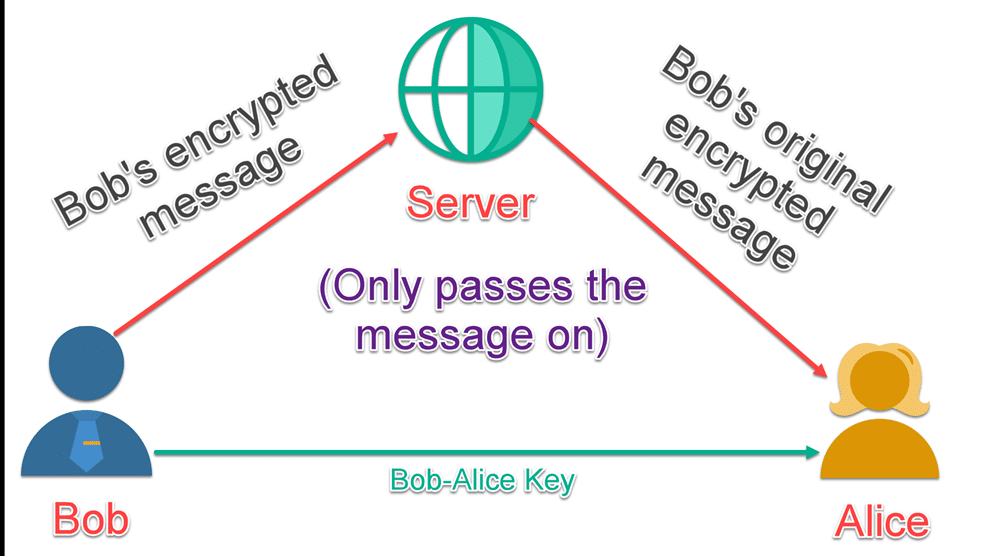
Now, end-to-end encryption has a key difference. On an end-to-end encrypted service, such as Signal, only you and the person you’re messaging have the ability to decrypt the message. The message still has to go through Signal’s servers, but those servers do not have the ability to decrypt the message.
Even if the government tried to force it to decrypt the messages, Signal wouldn’t be able to. In end-to-end encryption, decrypting a message requires your private key, which only your device has.
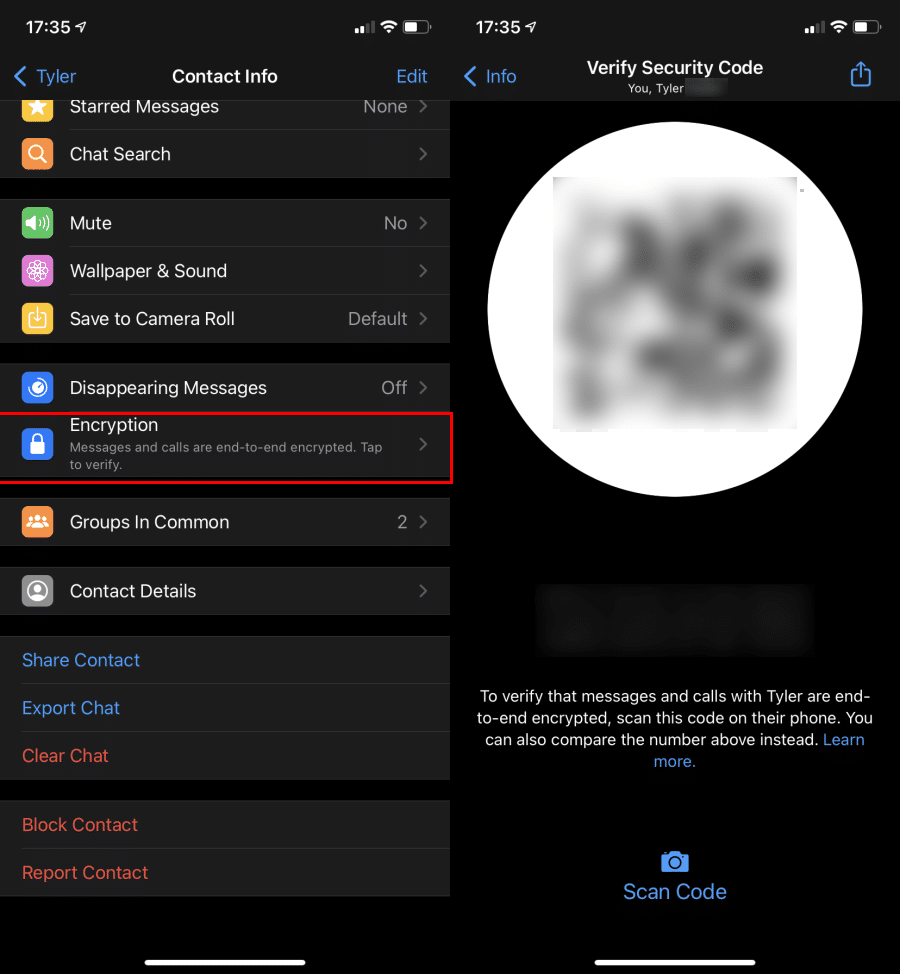
This is why apps that are end-to-end encrypted (including WhatsApp and Signal) only let you use them on one device at a time. Each device generates a private key, which your device uses to decrypt messages meant for it. While Signal and WhatsApp offer web apps, these are just mirrors of the app on your phone. You can’t use them unless your phone is connected to your PC.
End-to-end encryption also makes it more difficult for an attacker to tamper with the message, which is known as a man-in-the-middle attack. With the client-server model example, Facebook could take your message, change it, and deliver a modified version of what you said to the recipient. Neither of you would know this had happened.
With end-to-end encryption, any attempts to change the encrypted message will result in it in arriving as complete gibberish. This would alert the recipient that the message was tampered with in transit.
End-to-End Encryption Isn’t Perfect
While end-to-end encryption provides great security for messaging and other purposes, it still has some potential pitfalls. One of them is that while it protects the contents of your communication, the fact that you communicated with someone is still visible. Thus, it would still be possible to prove that you talked to a shady individual using an end-to-end encrypted service.
The more relevant factor is that end-to-end encrypted messages are only as secure as the device you access them on. This is because once messages arrive on your device, they are decrypted so you can read them.
Say you use Signal for end-to-end encrypted messages, but don’t have a passcode on your phone. Anyone who picked up your device would be able to open Signal and read all your messages, which obviously isn’t secure.
This means that you must be sure to keep your devices properly secured. Intruders, malware, or other forms of attack could allow your messages to be compromised. The same goes for whomever you’re talking to. If someone stole their phone and were able to unlock it, they could read all your communications.
Finally, end-to-end encryption could also be broken by a backdoor, which is a secret way of bypassing encryption implemented by the owner. You might not even be aware that the company behind a supposedly secure service is able to break the encryption and view your messages whenever it wants.
End-to-End Encryption Keeps Communication Private
Now you know the basics of how end-to-end encryption protects your communication. By only allowing the two devices communicating to decrypt the messages, you cut out the chance of a server in the middle compromising your privacy.
When you message someone and want to keep it private, you should stick with a service that offers end-to-end encryption. Compared to insecure methods like SMS and apps that aren’t end-to-end encrypted, they’re a much smarter choice. If you use an iPhone, the built-in iMessage is an end-to-end encrypted service already available to you.