Passwordstate, a password manager offered by Australian company Click Studios, recently made headlines for suffering a major security breach. While high-profile attacks on software have been unfortunately common in recent months, this instance is especially dangerous since it resulted in compromised credentials for many thousands of users.
Let’s look at what happened in the Passwordstate breach, how other password managers can prevent it from happening to them, and why password managers are still important.
Passwordstate’s Security Breach
Passwordstate is a password manager, designed for generating and securing secure passwords that its users don’t have to remember. This particular tool is aimed at enterprises, as it includes features like administration based on roles, event auditing, and compliance reporting.
In late April 2021, Click Studios alerted its users that the software had suffered an intrusion between April 20th and 22nd 2021 that was active for about 28 hours. Attackers were able to compromise the app’s update functionality to deliver a tampered DLL file to affected computers, during the process of an upgrade.
Once that file ran on a computer, it extracted data from the Passwordstate application and sent it to the attackers’ server. The data included usernames and passwords, names of all running processes, domain names, computer names, and more.
Click Studios states that its own servers were not compromised, and as of April 22, the hackers’ server was no longer available. It’s not known at this time whether the attackers turned off their own server, or if someone fighting back was able to take it offline.
Security researchers have dubbed this malware “Moserpass.” It’s not known who’s responsible for the attack or exactly how they compromised the update mechanism.
Phishing Follow-Up and Company Response
Unfortunately, a few days after this happened, Click Studios warned that attackers were also employing phishing attacks. Because customers had posted screenshots of legitimate correspondence from the company on social media, bad actors were able to better impersonate this communication.
They sent emails claiming that the recipient needs to download an urgent fix for the Passwordstate hack. Of course, this is bogus, and installing that file will only lead to further infection from the attackers’ malware.
IMPORTANT — Passwordstate warns its password management #software customers of ongoing #phishing attacks against after the recent data breach.
Read: https://t.co/lpf5Oa6pWr#infosec #cybersecurity #hacking
— The Hacker News (@TheHackersNews) April 30, 2021
This is the most recent supply chain attack in a string of similar cases. Like the Solarwinds hack a few months ago, supply chain attacks hit a company through one of the other firms it does business with. In this case, PasswordState could be used by an organization you work with, like a technology vendor. If that vendor stores login information for your company, you could be impacted by this without using the software directly.
Obviously, having passwords stolen in large numbers is extremely dangerous. This is especially the case with Passwordstate—since it’s an enterprise password manager, companies likely store credentials for firewalls and other critical business apps. Changing all of these—and quickly—is a time-consuming task.
The company has advised anyone who upgraded their client during the times that the update mechanism was compromised to change all passwords stored with the service. It has also released a fix to patch this vulnerability.
Could Other Password Managers Suffer the Same Fate?
If you use a password manager (either for your own use or for business), this event might give you pause about continuing to do so. Could your password manager suffer a similar attack?
On the 1Password forums, a staff member elaborated on this topic. They mention that we don’t know for sure what specifically happened in this attack, but that “standard code-signing defenses and integrity checks” should have been able to prevent this.
There’s a lot of technical discussion in that post, which is worth checking out if you’re interested in this. But in summary, the representative says that 1Password has multiple checks during the update and install process to make sure that you are downloading a genuine copy of the software, that has not been tampered with, from 1Password’s servers.
1Password staff says that there is nothing users really need to do to protect against these attacks. The company is aware that these attacks can happen and has built steps into the upgrade process to reduce their likelihood. They advise that you should never bypass integrity checks on your system and that it’s best to download from app stores when possible.
The post also contains instructions for manually checking to make sure that your copy of 1Password is not compromised. In all, the company is fairly confident that the attack that worked on Passwordstate wouldn’t have been effective against 1Password.
Of course, that only goes for 1Password. If you use a different password manager, it’s a good idea to check and/or ask about the steps that the company takes to prevent similar issues.
We checked both the LastPass and Bitwarden forums and didn’t see any official communication from either company like with 1Password. LastPass did publish a blog post on April 25 titled How LastPass Keeps Your Business Safe, though the post makes no mention of this incident specifically.
Password Managers Are Still the Safest Option
You might be tempted to let this incident fool you into thinking that you shouldn’t use password managers. Of course, Passwordstate isn’t the first password manager to suffer a breach. LastPass in particular has had a few problems over the years, and other managers like 1Password, Dashlane, and RoboForm have ran into issues too.
However, even though password managers aren’t perfect, they are a huge net positive. There are far, far many more stories of security breaches that happen from weak passwords being broken than there are incidents of password managers being hacked. Verizon’s data breach reports have found that somewhere around 80% of security breaches involve compromised or weak passwords.
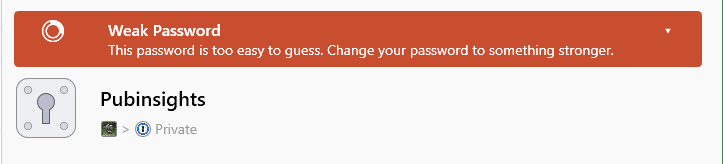
If you quit using a password manager because you’re worried about it being hacked, then go back to use the same password for every website, you’re trading a small chance of attack for one of the most common security risks. No piece of software is 100% bulletproof, but using them can still drastically increase your security.
Stick with a trusted password manager, like 1Password, that has strong checks in place to prevent break-ins. And in addition to strong passwords, make sure you follow other important security measures, like securing your accounts with two-factor authentication and not reusing passwords on multiple sites. That way, if any one tool you use is compromised, it won’t be catastrophic for your overall security health.
Take a look at our vital security practices for everyone to learn more.