In July 2022, several security companies found that malicious actors were impersonating them to send out emails with the intent to trick users. While the exact results of this campaign aren’t known, it’s a good opportunity to learn from scammers’ tricks to protect yourself in the future.
Let’s look at this malicious campaign and how trusted company names were abused.
The Fake CrowdStrike Email
If you’re not familiar, CrowdStrike is a security company that offers antivirus, breach protection, and similar security software. We’ve discussed the benefits of CrowdStrike EDR in the past, and use this software for many of our clients.
On July 8, 2022, CrowdStrike published details about a campaign impersonating it. Below is an image of the email that many people received, which claimed to come from the company. While CrowdStrike wasn’t the only company used in this campaign, it serves as a good representation.
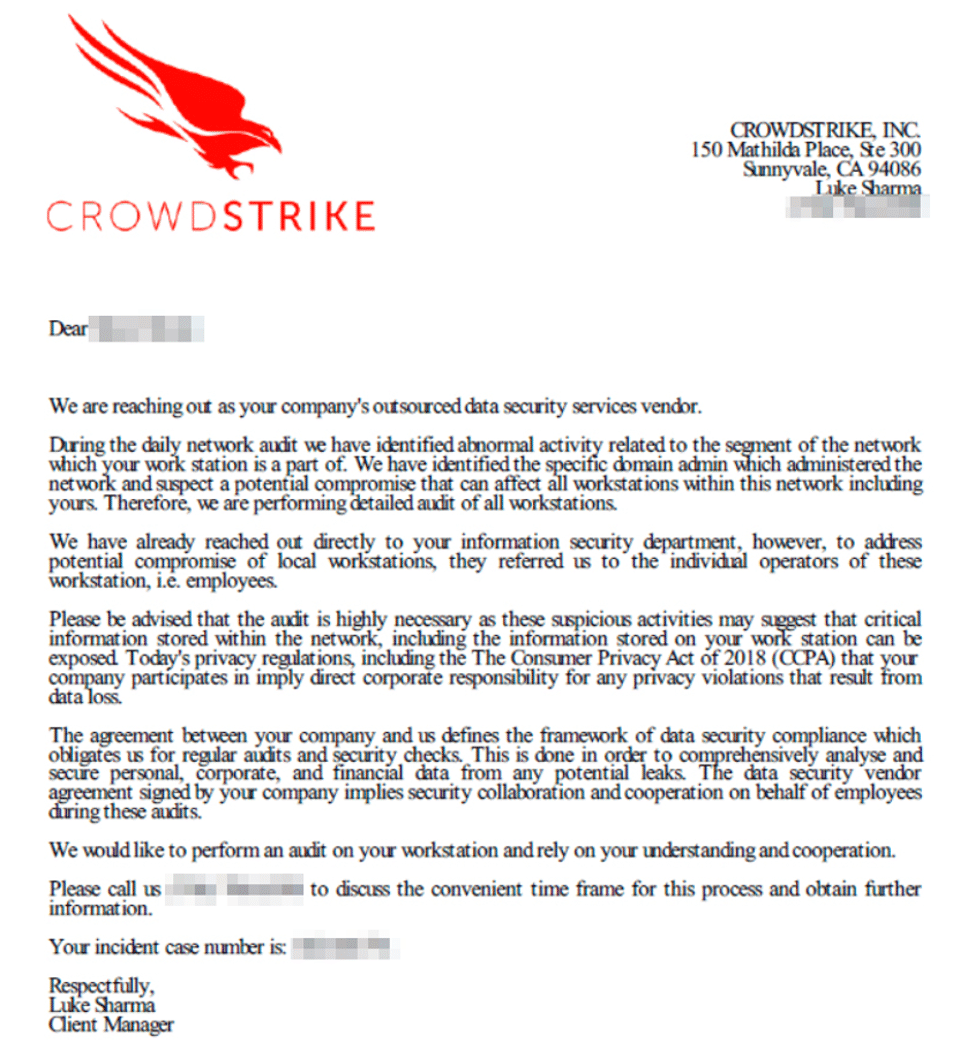
As you can see in the message, the crux of this attack revolves around asking the potential victim to call a phone number. This is known as a callback scam, as the goal of the email is for you to call this number without thinking.
It’s worth noting that callback scams can take other forms. Another popular method is for a scammer to call you and immediately hang up. The hope is that you call back—either out of curiosity or courtesy—and get hooked on the scam.
The Intended Attack
If you were to call the number in this phoney email, you wouldn’t get CrowdStrike on the phone. Rather, you would reach someone pretending to be from the company.
CrowdStrike’s blog post surmises that the attackers would then guide you through the process of installing legitimate remote desktop software (such as TeamViewer) so they can control your machine. From there, they could take any number of actions.
This would most likely be installing ransomware on your machine and demanding payment. But they could also try to spread to other computers on your network by abusing security software, or even monitor your activity over time.
We’ve discussed before how ransomware is a serious threat, and this is yet another way that criminals try to exploit people with it.
Learning From This Attack
While the details of this malicious campaign are simple, it reinforces key principles that you can use to protect yourself from future attempts like this. There are several factors to take away.
First, in the event of a breach, a company like CrowdStrike would not reach out to users directly like this. When the software detects a threat on the company’s network, it will let the IT staff know, not the user.
Second, even if the email was legitimate, security companies would not ask you to reach out to them by phone. A legitimate message would direct you towards the software’s dashboard so you can see what happened and take action.
Third, this email has common factors of a phishing attack. There are several instances of typos and awkward grammar, including:
- “we are performing detailed audit”
- “the individual operators of these workstation, i.e. employees” both has a typo and sounds robotic.
- The UK spelling “analyse” is used, which an American company would not do.
- “discuss the convenient time frame”
Additionally, the third paragraph is a run-on sentence, and CCPA stands for California Consumer Privacy Act, not “The Consumer Privacy Act”.
The contents of the message also don’t make sense if you think about them. The second paragraph says that they’ve contacted your security department but that the department asked them to contact employees directly. No security department would ever do this. And of course, if you looked up the number in the message, you’d see that it doesn’t belong to CrowdStrike.
Finally, the email puts pressure on you to act quickly. It mentions regulations and uses phrases like “highly necessary” and “direct corporate responsibility” to make it sound scarier. They’re hoping that you act without thinking it through.
Protect Against Malicious Campaigns
As we’ve seen, with a sharp eye, you can see through these scams and know when someone is trying to trick you. Whether you notice grammatical errors or know instinctively not to call numbers or click links in unsolicited emails, it’s important to stay vigilant against these attacks.
If you ever receive a message and aren’t sure if it’s legitimate, talk with your IT staff about it before responding. It’s also worth talking to them about what kind of correspondence you should expect. For example, if you knew that you’ll never be asked to call a phone number in response to an attack, you can disregard any such requests as dangerous.
For more tips, be aware of the major signs of phone call scams.